
Technical interviews are a crucial part of the hiring process in the Norwegian IT sector. These interviews are designed to assess a candidate’s technical skills, problem-solving abilities, and suitability for the role. Companies in Norway place a high value on practical knowledge and the ability to apply technical expertise to real-world scenarios.
During a technical interview, candidates can expect to encounter a variety of tech interview questions that test their understanding of programming languages, algorithms, data structures, and system design. These questions are intended to evaluate both theoretical knowledge and practical application. For roles such as software developers, data scientists, and IT consultants, demonstrating proficiency through coding exercises, case studies, and technical problem-solving is essential.
How to Prepare for Tech Interview?
Preparing for a tech interview is crucial for securing a job in the competitive Norwegian IT sector. Here are some effective strategies to ensure you are well-prepared:
1. Understand the Job Requirements
Start by thoroughly understanding the job description and the specific technical skills required for the role. This helps you focus your preparation on the most relevant areas.
2. Review Core Concepts
Make sure to review the core concepts related to your field. For software development roles, this includes data structures, algorithms, system design, and programming languages. For other IT roles, focus on the specific technical knowledge pertinent to the position.
3. Practice Coding
Regularly practice coding problems on platforms like LeetCode, HackerRank, and CodeSignal. This will help you get comfortable solving problems under time constraints, which is a common aspect of technical interviews.
4. Study Common Tech Interview Questions
Familiarize yourself with common tech interview questions that are likely to come up during the interview. These questions often cover a range of topics from basic programming to advanced problem-solving scenarios.
5. Mock Interviews
Participate in mock interviews to simulate the actual interview experience. This can help reduce anxiety and improve your performance. Utilize resources that offer the best tech interview prep, such as Pramp, Interviewing.io, and professional coaching services.
6. Understand the Company’s Tech Stack
Research the company’s technology stack and tools they use. Tailoring your preparation to align with the company’s specific technologies can give you an edge during the interview.
7. Develop Soft Skills
Technical skills are critical, but companies also look for candidates with strong communication and problem-solving abilities. Practice explaining your thought process clearly and concisely.
8. Prepare for Behavioral Questions
Be ready to answer behavioral questions that assess your soft skills, teamwork, and cultural fit. Reflect on your experiences and how they relate to the job you are applying for.
9. Network and Seek Advice
Connect with professionals working in your desired field and ask for advice on preparing for interviews. Networking can also help you understand what to expect and give you insights into the company’s interview process.
10. Stay Updated
Keep yourself updated with the latest trends and developments in the tech industry. This shows your passion and commitment to staying relevant in your field.
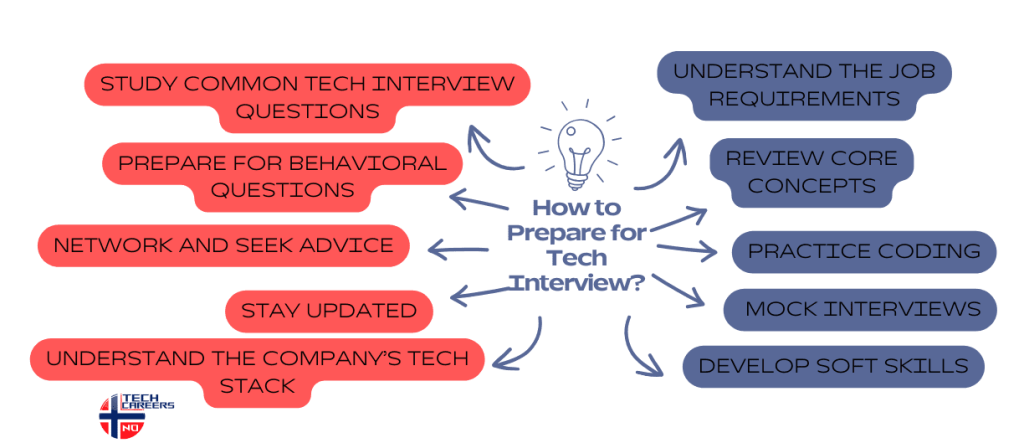
By following these strategies and leveraging resources for tech interview preparation, you can enhance your readiness for technical interviews. Whether you are aiming for jobs for foreigners in Norway or seeking to advance in your current career, thorough preparation is key to success.
Tech Questions and Answers for Different IT Roles
What design patterns have you used in PHP projects?
- Answer: Common design patterns include Singleton, Factory, Strategy, Observer, and MVC.
How do you handle error reporting in PHP?
- Answer: Use error_reporting() function, set display_errors directive in php.ini, and log errors using error_log().
Can you explain dependency injection in PHP?
- Answer: Dependency Injection involves passing dependencies (services) into a class instead of the class creating them, promoting loose coupling.
How do you optimize PHP performance?
- Answer: Techniques include using opcode caching, optimizing database queries, minimizing server requests, using efficient data structures, and employing content delivery networks (CDNs).
What is the difference between a role and a profile in Salesforce?
- Answer: Profiles control what users can do (permissions), while roles control what users can see (data visibility).
How do you handle governor limits in Salesforce?
- Answer: Optimize SOQL queries, use bulk processing, avoid nested loops, and use asynchronous processing when possible.
Can you explain the use of triggers in Salesforce?
- Answer: Triggers are used to perform custom actions before or after events to records in Salesforce, such as insertions, updates, or deletions.
What are Salesforce Governor Limits?
- Answer: Governor limits are runtime limits enforced by the Salesforce platform to ensure efficient processing of operations.
What are the differences between CSS Grid and Flexbox?
- Answer: CSS Grid is two-dimensional (rows and columns), while Flexbox is one-dimensional (either row or column).
How do you optimize a web page for performance?
- Answer: Minimize HTTP requests, use lazy loading for images, compress and cache assets, optimize CSS and JavaScript, and use a content delivery network (CDN).
What is the virtual DOM and how does it work in React?
- Answer: The virtual DOM is a lightweight copy of the actual DOM. It allows React to batch updates and render changes efficiently.
Can you explain the concept of responsive design?
- Answer: Responsive design ensures that a web page looks good and functions well on devices of various sizes and orientations by using flexible grids, layouts, images, and CSS media queries.
What are the benefits of using TypeScript over JavaScript?
- Answer: TypeScript provides static type checking, early bug detection, enhanced code readability, better refactoring, and improved IDE support.
Can you explain TypeScript generics?
- Answer: Generics allow you to create reusable components that work with any data type while maintaining type safety.
How do you handle asynchronous operations in TypeScript?
- Answer: Use async/await syntax for better readability and error handling, along with Promises and callbacks when necessary.
What is the difference between interface and type in TypeScript?
- Answer: Both are used to define custom types, but interfaces can be extended or implemented by classes, while types are more versatile with union types and can be used to define primitive types.
What are Python decorators and how do you use them?
- Answer: Decorators are functions that modify the behavior of another function or class. They are used with the @decorator_name syntax above a function definition.
How do you manage dependencies in a Python project?
- Answer: Use a virtual environment and manage dependencies with pip and requirements.txt files, or use a tool like poetry.
Can you explain the difference between deepcopy and copy?
- Answer: copy.copy() creates a shallow copy of an object, while copy.deepcopy() creates a deep copy, including recursively copying objects found within the original object.
What are Python’s built-in data structures?
- Answer: Lists, dictionaries, sets, and tuples are the primary built-in data structures in Python.
What software development methodologies are you familiar with?
- Answer: Common methodologies include Agile, Scrum, Kanban, Waterfall, and DevOps.
How do you ensure code quality and maintainability?
- Answer: Use code reviews, automated testing, continuous integration, adherence to coding standards, and proper documentation.
Can you explain SOLID principles?
- Answer: SOLID is an acronym for five design principles: Single Responsibility, Open/Closed, Liskov Substitution, Interface Segregation, and Dependency Inversion.
How do you handle version control in your projects?
- Answer: Use version control systems like Git, following best practices such as feature branching, pull requests, and commit messages.
What is your approach to debugging code?
- Answer: Identify the problem, use logging and breakpoints, isolate the issue, test fixes incrementally, and review relevant documentation.
How do you manage database migrations?
- Answer: Use migration tools like Flyway, Liquibase, or ORM-specific migration systems, and maintain version control of migration scripts.
Can you explain the concept of microservices architecture?
- Answer: Microservices architecture involves breaking down an application into small, independent services that communicate over a network, each responsible for a specific functionality.
What are some common security practices you follow in development?
- Answer: Use secure coding practices, validate and sanitize input, use parameterized queries to prevent SQL injection, encrypt sensitive data, and perform regular security audits.
What is the difference between UX and UI design?
- A.: UX Design (User Experience Design) focuses on the overall feel of the experience. It is about enhancing user satisfaction by improving the usability, ease of use, and pleasure provided in the interaction between the user and the product. UX design involves research, wireframing, prototyping, and testing.
- UI Design (User Interface Design) focuses on the look and layout. It is about creating interfaces in software or computerized devices with a focus on looks or style. UI design includes designing the graphical layout of an application, creating buttons, icons, spacing, typography, and color schemes.
Can you explain the concept of ‘User-Centered Design’?
- A.: User-Centered Design (UCD) is an iterative design process in which designers focus on the users and their needs in each phase of the design process. UCD involves user research, persona creation, usability testing, and feedback loops to ensure that the final product is highly usable and meets user expectations.
What is a wireframe, and why is it important?
- A.: A wireframe is a low-fidelity, simplified outline of a product or a screen, focusing on layout and content placement rather than colors and graphics. Wireframes are important because they allow designers and stakeholders to focus on the structure and functionality of the interface without getting distracted by visual design elements. They serve as a blueprint for the design process and help in communicating ideas clearly.
What is the purpose of user personas in UX design?
- A.: User personas are fictional characters created based on user research to represent different user types that might use a product or service in a similar way. They help designers and stakeholders understand the target audience’s needs, experiences, behaviors, and goals. Personas guide design decisions by keeping the focus on user needs and ensuring the product is user-friendly.
What are the primary steps to securing a corporate network?
- A.: Securing a corporate network involves several key steps: implementing strong firewalls, using intrusion detection and prevention systems, regular patching and updating of software, employing strong access controls, encrypting sensitive data, conducting regular security audits, and educating employees about security best practices.
How can a company defend against phishing attacks?
- A.: To defend against phishing attacks, companies should implement email filtering solutions, conduct regular employee training on recognizing phishing attempts, employ multi-factor authentication, regularly update and patch systems, and simulate phishing attacks to test and improve employee awareness.
What is the importance of regular security audits?
- A.: Regular security audits are crucial because they help identify vulnerabilities, ensure compliance with security policies, assess the effectiveness of security controls, and provide insights into areas that need improvement. Audits also help in maintaining a robust security posture and mitigating potential threats before they can be exploited.
Can you explain the concept of Zero Trust Architecture?
- A.: Zero Trust Architecture is a security model that assumes no implicit trust and requires verification of every device, user, and network attempting to access resources. It emphasizes strict identity verification, micro-segmentation, least-privilege access, and continuous monitoring to ensure that only authorized entities can access critical data and systems.
How does encryption protect data, and what are its limitations?
- A.: Encryption protects data by converting it into a coded format that can only be deciphered with the correct decryption key. This ensures that even if data is intercepted, it cannot be read by unauthorized parties. However, encryption is not foolproof; it relies on secure key management, and if keys are compromised, so is the data. Additionally, encryption doesn’t protect data from being deleted or corrupted.
What is the difference between Agile and Waterfall methodologies?
- A: Agile is an iterative approach that allows for more flexibility and continuous improvement, involving constant feedback and collaboration. Waterfall is a linear, sequential approach where each phase must be completed before the next begins, making it more rigid but easier to manage for well-defined projects.
How do you handle scope creep in a project?
- A: Scope creep can be managed by clearly defining the project scope from the beginning, implementing a formal change control process, regularly communicating with stakeholders, and prioritizing project tasks to ensure that essential features are completed first.
What are some key performance indicators (KPIs) for measuring project success?
- A: Common KPIs include project completion on time, staying within budget, meeting quality standards, achieving stakeholder satisfaction, and meeting project objectives and deliverables.
What is risk management in project management?
- A: Risk management involves identifying, assessing, and prioritizing risks followed by coordinated efforts to minimize, monitor, and control the probability or impact of unfortunate events. It includes risk identification, analysis, response planning, and monitoring.
Can you explain the concept of the project management triangle?
- A: The project management triangle, also known as the triple constraint, refers to the three primary constraints in any project: scope, time, and cost. Balancing these constraints is crucial for project success, as changes in one constraint will affect the others.
What tools do you use for project management?
- A: Popular project management tools include Jira, Trello, Asana, Microsoft Project, and Monday.com. These tools help in task management, collaboration, time tracking, and reporting.
These questions and answers are designed to help you prepare for technical interviews across various IT roles. Each set focuses on the specific skills and knowledge required for the respective position.
Download a List of 100 Norwegian Interview Questions and Answers
Enhance your interview preparation with our all-inclusive guide. Download your free copy today and excel in your next interview!
Behavioral, Situational and General Questions
Can you describe a time when you had to troubleshoot a difficult technical issue in your previous IT job in Norway?
- What was the issue, and how did you resolve it?
Tell me about a project where you had to collaborate with a team remotely. How did you ensure effective communication and project completion?
- This is particularly relevant for IT jobs in Norway, where remote work is common.
Have you ever faced a situation where you had to learn a new technology quickly for your job in Norway?
- How did you approach the learning process, and what was the outcome?
Describe a time when you had to handle multiple IT tasks simultaneously in a high-pressure environment.
- How did you prioritize and manage your workload?
Can you give an example of when you improved a process or system in your IT role in Norway?
- What changes did you make, and what were the results?
Imagine you are working on a critical IT project in Norway, and you encounter a major security breach.
- How would you handle the situation?
You are leading an IT team on a project with a tight deadline. One of your team members is consistently missing their deadlines.
- How would you address this issue to ensure the project stays on track?
You are tasked with migrating a company’s data to a new system, and you discover that the data is corrupted.
- What steps would you take to resolve this issue?
Suppose you are working on an IT support desk in Norway, and you receive multiple urgent support tickets simultaneously.
- How would you prioritize these tickets?
You are asked to implement a new software solution, but some team members are resistant to change.
- How would you manage their concerns and ensure a smooth implementation?
What motivated you to pursue a career in IT jobs in Norway?
- What do you find most appealing about working in this field?
What are the most important technical skills you possess that make you a good fit for IT jobs in Norway?
- Can you provide examples of how you have applied these skills?
How do you stay updated with the latest trends and technologies in the IT industry, particularly in Norway?
- Can you share any resources or strategies you use?
What do you believe are the biggest challenges facing the IT industry in Norway today?
- How do you think these challenges can be addressed?
Why do you want to work for our company in Norway, and what do you know about our IT projects?
- How do you think your background and skills align with our needs?
These questions are designed to gauge a candidate’s experience, problem-solving abilities, and fit for IT jobs in Norway.
Ready to take your IT career to the next level in Norway?
Start preparing for your technical interviews today! Leverage these strategies, practice diligently, and stay updated with the latest industry trends to secure your dream job. Begin your journey now and make your mark in the Norwegian IT sector.


 Previous Post
Previous Post Next Post
Next Post